CCNA Practice Exam 1
Quiz Summary
0 of 101 Questions completed
Questions:
Information
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading…
You must sign in or sign up to start the quiz.
You must first complete the following:
Results
Results
0 of 101 Questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 point(s), (0)
Earned Point(s): 0 of 0, (0)
0 Essay(s) Pending (Possible Point(s): 0)
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- Current
- Review
- Answered
- Correct
- Incorrect
-
Question 1 of 101
1. Question
How does CAPWAP communicate between an access point in local mode and a WLC?
CorrectIncorrect -
Question 2 of 101
2. Question
Which of the following is not an advantage of a next generation firewall (NGFW)?
CorrectIncorrect -
Question 3 of 101
3. Question
What is a characteristic of spine-and-leaf architecture?
CorrectIncorrect -
Question 4 of 101
4. Question
Which of the following descriptions are related to the Puppet technology? (Choose two).
CorrectIncorrect -
Question 5 of 101
5. Question
Which two reasons can cause the late collision counter to increment on an Ethernet interface? (Choose two).
CorrectIncorrect -
Question 6 of 101
6. Question
What are two common TCP applications? (Choose two).
CorrectIncorrect -
Question 7 of 101
7. Question
What is the difference regarding reliability and communication type between TCP and UDP?
CorrectIncorrect -
Question 8 of 101
8. Question
Given a subnet mask of 255.255.255.224, which of the following addresses can be assigned to network hosts? (Choose three).
CorrectIncorrect -
Question 9 of 101
9. Question
Given an IP address of 192.168.1.42 255.255.255.248, what is the subnet address?
CorrectIncorrect -
Question 10 of 101
10. Question
A network engineer needs to configure a branch office for 82 hosts. What is the most efficient use of a subnet mask?
CorrectIncorrect -
Question 11 of 101
11. Question
Which three network addresses are reserved for private network use? (Choose three).
CorrectIncorrect -
Question 12 of 101
12. Question
An IPv6 multicast address always begins with which Hexadecimal digits?
CorrectIncorrect -
Question 13 of 101
13. Question
Identify the four valid IPv6 addresses. (Choose four).
CorrectIncorrect -
Question 14 of 101
14. Question
During which lightweight access point operation state does the device poll the wireless LAN controller (WLC) for information such as QoS rules, SSIDs, and security parameters?
CorrectIncorrect -
Question 15 of 101
15. Question
An engineer must configure a WLAN using the strongest encryption type for WPA2-PSK. Which cipher fulfills the configuration requirement?
CorrectIncorrect -
Question 16 of 101
16. Question
Which mode of Wi-Fi protected access (WPA) is also referred to as enterprise mode?
CorrectIncorrect -
Question 17 of 101
17. Question
What are two fundamentals of virtualization? (Choose two).
CorrectIncorrect -
Question 18 of 101
18. Question
A MAC address is _____ bits long, and expressed in _____?
CorrectIncorrect -
Question 19 of 101
19. Question
All 30 users on a single floor of a building are complaining about network slowness. After investigating the access switch, the network administrator notices that the MAC address table is full (10,000 entries) and all traffic is being flooded out of every port. Which action can the administrator take to prevent this from occurring?
CorrectIncorrect -
Question 20 of 101
20. Question
A Cisco switch has 8 PCs connected and the switch is in its default configuration. The switch also connects to a Cisco router. How many collision domains
are there?CorrectIncorrect -
Question 21 of 101
21. Question
An engineer is asked to protect unused ports that are configured in the default VLAN on a switch. Which two steps will fulfill the request? (Choose two).
CorrectIncorrect -
Question 22 of 101
22. Question
Assuming the default switch configuration, which VLAN range can be added, modified, and removed on a Cisco switch?
CorrectIncorrect -
Question 23 of 101
23. Question
On a corporate network, hosts on the same VLAN can communicate with each other, but they cannot communicate with hosts on different VLANs. What is needed to allow communication between the VLANs?
CorrectIncorrect -
Question 24 of 101
24. Question
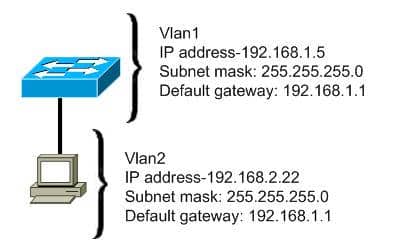
Refer to the exhibit. A host is connected to switch port fa0/3. The host and switch have been fully configured for IP connectivity as shown. However, the indicator LED on switch port fa0/3 is not on, and the host cannot communicate with any other hosts including those connected to VLAN 2 on the same switch. Based on the given information, what is the problem?
CorrectIncorrect -
Question 25 of 101
25. Question
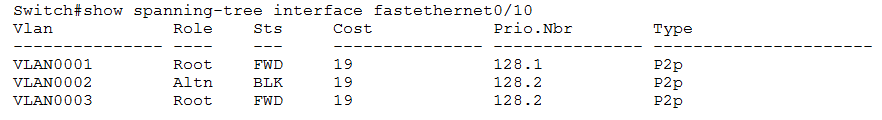
Refer to the exhibit. Given the output shown from this Cisco Catalyst 2950, what is the reason that interface FastEthernet 0/10 is not the root port for VLAN 2?
CorrectIncorrect -
Question 26 of 101
26. Question
Three switches are connected to one another via trunk ports. Assuming the default switch configuration, which switch is elected as the root bridge for the spanning-tree instance of vlan 1?
CorrectIncorrect -
Question 27 of 101
27. Question
What are three advantages of VLANs? (Choose three).
CorrectIncorrect -
Question 28 of 101
28. Question
Which statements accurately describe CDP? (Choose three).
CorrectIncorrect -
Question 29 of 101
29. Question
You are the network administrator for your company and have configured Cisco Discovery Protocol (CDP) in your network. You recently noticed that when devices send large numbers of CDP neighbor announcements, some devices are crashing. You decide to disable CDP on the router. Which command should you use to achieve the objective?
CorrectIncorrect -
Question 30 of 101
30. Question
Which command is used to enable LLDP globally on a Cisco IOS ISR?
CorrectIncorrect -
Question 31 of 101
31. Question
Which command should you enter to configure an LLDP delay time of 5 seconds?
CorrectIncorrect -
Question 32 of 101
32. Question

Refer to the exhibit. Based on the LACP neighbor status, in which mode is the SW1 port channel configured?
CorrectIncorrect -
Question 33 of 101
33. Question
What is a difference between local AP mode and FlexConnect AP mode?
CorrectIncorrect -
Question 34 of 101
34. Question
A network administrator cannot connect to a remote router by using SSH. Part of the show interfaces command is shown.
router#show interfaces Serial0/1/0 is up, line protocol is down
At which OSI layer should the administrator begin troubleshooting?
CorrectIncorrect -
Question 35 of 101
35. Question
Which QoS Profile is selected in the GUI when configuring a voice over WLAN deployment?
CorrectIncorrect -
Question 36 of 101
36. Question
Match the Cisco default administrative distance to the appropriate routing protocol or route.
Sort elements
- directly connected
- static route referencing IP address of next hop
- internal EIGRP route
- OSPF
- RIP
-
0
-
1
-
90
-
110
-
120
CorrectIncorrect -
Question 37 of 101
37. Question
What is the default Reference Bandwidth used by OSPF to calculate Cost?
CorrectIncorrect -
Question 38 of 101
38. Question
What are two reasons for an engineer to configure a floating static route? (Choose two).
CorrectIncorrect -
Question 39 of 101
39. Question
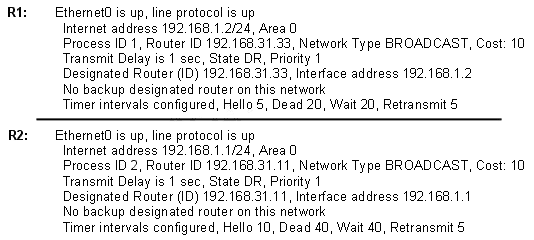
A network administrator is troubleshooting the OSPF configuration of routers R1 and R2. The routers cannot establish an adjacency relationship on their common Ethernet link. The graphic shows the output of the show ip ospf interface e0 command for routers R1 and R2. Based on the information in the graphic, what is the cause of this problem?
CorrectIncorrect -
Question 40 of 101
40. Question
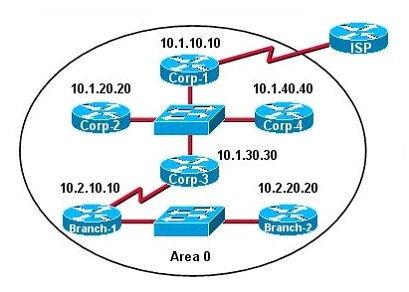
The internetwork infrastructure of company XYZ consists of a single OSPF area as shown in the graphic. There is concern that a lack of router resources is impeding internetwork performance. As part of examining the router resources, the OSPF DRs need to be known. All the router OSPF priorities are at the default and the router IDs are shown with each router. Which routers are likely to have been elected as DR? (Choose two).
CorrectIncorrect -
Question 41 of 101
41. Question
How does using the service password-encryption command on a router provide additional security?
CorrectIncorrect -
Question 42 of 101
42. Question

If configuring a static default route on the router with the ip route 0.0.0.0 0.0.0.0 10.13.0.1 120 command, how does the router respond?
CorrectIncorrect -
Question 43 of 101
43. Question
Which protocol is the Cisco proprietary implementation of FHRP?
CorrectIncorrect -
Question 44 of 101
44. Question
Identify the different types of NAT. (Choose three).
CorrectIncorrect -
Question 45 of 101
45. Question
In a Network Address Translation (NAT) configuration, what command is given (and in what configuration mode is it given) to specify that an interface is on the inside of a network?
CorrectIncorrect -
Question 46 of 101
46. Question
Which of the following commands is used to configure NTP client functionality on a Cisco router?
CorrectIncorrect -
Question 47 of 101
47. Question
Which of the following displays a JSON representation?
CorrectIncorrect -
Question 48 of 101
48. Question
What does the R stand for in CRUD?
CorrectIncorrect -
Question 49 of 101
49. Question
The main function of northbound APIs in the SDN architecture is to enable communication between which two areas of a network?
CorrectIncorrect -
Question 50 of 101
50. Question
Order the DHCP message types as they would occur between a DHCP client and a DHCP server.
-
DHCPDISCOVER
-
DHCPACK
-
DHCPREQUEST
-
DHCPOFFER
View Answers:
CorrectIncorrect -
-
Question 51 of 101
51. Question
DNS servers provide what service?
CorrectIncorrect -
Question 52 of 101
52. Question
Refer to the router output. What does the number 15 represent in this configuration?
snmp-server group SNMP v3 auth access 15
CorrectIncorrect -
Question 53 of 101
53. Question
What are three components that comprise the SNMP framework? (Choose three).
CorrectIncorrect -
Question 54 of 101
54. Question
What is the default Syslog facility level?
CorrectIncorrect -
Question 55 of 101
55. Question
Which Syslog message code indicates an emergency state where the system is unstable?
CorrectIncorrect -
Question 56 of 101
56. Question
Under what condition would the DHCP Relay Agent feature be required in order to make sure our network hosts are able to obtain an IP address through DHCP?
CorrectIncorrect -
Question 57 of 101
57. Question
What 8-bit field exists in IP packet for QoS?
CorrectIncorrect -
Question 58 of 101
58. Question
What Cisco WLAN QoS class is designed for normal traffic?
CorrectIncorrect -
Question 59 of 101
59. Question
Which QoS mechanism is most appropriate for giving priority treatment to voice or video packets?
CorrectIncorrect -
Question 60 of 101
60. Question
The process of attempting to exploit a weakness in a network after being given permission by the company is known as what?
CorrectIncorrect -
Question 61 of 101
61. Question
With a DHCP snooping configuration, which type of port designation would be used on an interface up-linked to a DHCP server?
CorrectIncorrect -
Question 62 of 101
62. Question
A network administrator is configuring ACLs on a Cisco router to allow traffic from hosts on networks 192.168.146.0, 192.168.147.0, 192.168.148.0, and 192.168.149.0 only. Which two ACL statements, when combined, would you use to accomplish this task? (Choose two).
CorrectIncorrect -
Question 63 of 101
63. Question
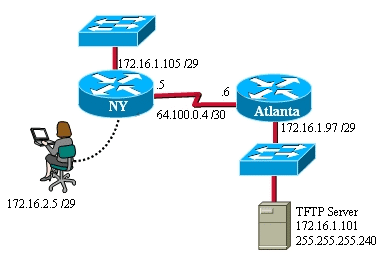
Refer to the exhibit. A TFTP server has recently been installed in the Atlanta office. The network administrator is located in the NY office and has made a console connection to the NY router. After establishing the connection, they are unable to backup the configuration file and IOS of the NY router to the TFTP server. What is the cause of this problem?
CorrectIncorrect -
Question 64 of 101
64. Question
What is the effect of this configuration?
line vty 0 4
password todd
login
transport input sshCorrectIncorrect -
Question 65 of 101
65. Question
To prevent users from plugging a host into a Switch port, which command is used to enable port security on a Switch?
CorrectIncorrect -
Question 66 of 101
66. Question
When a site-to-site VPN is used, which protocol is responsible for the transport of user data?
CorrectIncorrect -
Question 67 of 101
67. Question
CorrectIncorrect -
Question 68 of 101
68. Question
What is the primary difference between AAA authentication and authorization?
CorrectIncorrect -
Question 69 of 101
69. Question
What are the two most commonly used authentication factors in multifactor authentication? (Choose two)
CorrectIncorrect -
Question 70 of 101
70. Question
On a Cisco router which two router modes can be protected by a password? (Choose two).
CorrectIncorrect -
Question 71 of 101
71. Question
Which command can you enter to configure a local username with an encrypted password and EXEC mode user privileges?
CorrectIncorrect -
Question 72 of 101
72. Question
What method of data collection used by Cisco DNA Center follows a push-based model?
CorrectIncorrect -
Question 73 of 101
73. Question
How do traditional campus device management and Cisco DNA Center device management differ in regard to deployment?
CorrectIncorrect -
Question 74 of 101
74. Question
What is a benefit of using a Cisco Wireless LAN Controller?
CorrectIncorrect -
Question 75 of 101
75. Question
What statement about Link Aggregation when implemented on a Cisco Wireless LAN controller is true?
CorrectIncorrect -
Question 76 of 101
76. Question
A network engineer is configuring an OSPFv2 neighbor adjacency. Which of the following parameters must be unique regarding OSPF routers? (Choose two).
CorrectIncorrect -
Question 77 of 101
77. Question
A router is running three routing processes: RIP, OSPF, and EIGRP, each configured with default characteristics. Each process learns a route to the same remote network. If there are no static routes to the destination and none of the routes were redistributed, which route will be placed in the IP routing table?
CorrectIncorrect -
Question 78 of 101
78. Question
An engineer configured an OSPF neighbor as a designated router. Which state verifies the designated router is in the proper mode?
CorrectIncorrect -
Question 79 of 101
79. Question
Which statement about the native VLAN in 802.1Q is false?
CorrectIncorrect -
Question 80 of 101
80. Question
What is the primary effect of the spanning-tree portfast command?
CorrectIncorrect -
Question 81 of 101
81. Question
What does RSTP use for a fast converging backup for the root port in RSTP?
CorrectIncorrect -
Question 82 of 101
82. Question
In a switched environment, what does the IEEE 802.1Q standard describe?
CorrectIncorrect -
Question 83 of 101
83. Question
What term is assigned to an untagged VLAN on an IEEE 802.1Q trunk?
CorrectIncorrect -
Question 84 of 101
84. Question
Which of these represents an IPv6 link-local address?
CorrectIncorrect -
Question 85 of 101
85. Question
Which two endpoint measures are used to minimize the chances of falling victim to phishing and social engineering attacks? (Choose two)
CorrectIncorrect -
Question 86 of 101
86. Question
A workstation has just resolved a browser URL to the IP address of a server. What protocol will the workstation now use to determine the destination MAC address to be placed into frames directed toward the server?
CorrectIncorrect -
Question 87 of 101
87. Question
An organization has decided to start using cloud-provided services. Which cloud service allows the organization to install its own operating system on a virtual machine?
CorrectIncorrect -
Question 88 of 101
88. Question
How can you ensure that only the MAC address of a server is allowed by switch port Fa0/1?
CorrectIncorrect -
Question 89 of 101
89. Question
What feature permits the dynamic learning of the static port security addresses?
CorrectIncorrect -
Question 90 of 101
90. Question
A switch receives a frame on one of its ports. There is no entry in the MAC address table for the destination MAC address. What will the switch do with the frame?
CorrectIncorrect -
Question 91 of 101
91. Question
A host wants to send a message to another host that has the IP address 115.99.80.157. IP does not know the hardware address of the destination device. Which protocol can be used to discover the MAC address?
CorrectIncorrect -
Question 92 of 101
92. Question
What are two benefits of network automation? (Choose two).
CorrectIncorrect -
Question 93 of 101
93. Question
What plane of operation would OSPF belong to in a Cisco DNA Center SDN environment?
CorrectIncorrect -
Question 94 of 101
94. Question
Which of the following commands will enable a global IPv6 address based on the Modified EUI-64 format interface ID?
CorrectIncorrect -
Question 95 of 101
95. Question
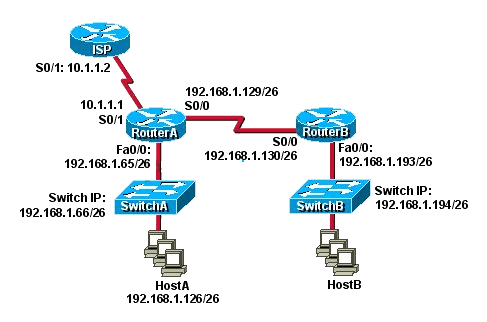
Refer to the exhibit. Which default gateway address should be assigned to HostA?
CorrectIncorrect -
Question 96 of 101
96. Question
Which command will set the default gateway to 192.168.12.1 on a Cisco switch?
CorrectIncorrect -
Question 97 of 101
97. Question
Thanks to OSPF. your router has several matches for a destination prefix in its routing table. Which will it use to forward packets?
CorrectIncorrect -
Question 98 of 101
98. Question
What are three characteristics of the OSPF routing protocol? (Choose three).
CorrectIncorrect -
Question 99 of 101
99. Question
What two things will a router do when running a distance vector routing protocol? (Choose two).
CorrectIncorrect -
Question 100 of 101
100. Question
CorrectIncorrect -
Question 101 of 101
101. Question
What WAN design ensures that your users can still access the internet even in the event of a catastrophic failure at your main ISP?
CorrectIncorrect