Cisco ENCOR Practice Exam
Quiz Summary
0 of 102 Questions completed
Questions:
Information
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading…
You must sign in or sign up to start the quiz.
You must first complete the following:
Results
Results
0 of 102 Questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 point(s), (0)
Earned Point(s): 0 of 0, (0)
0 Essay(s) Pending (Possible Point(s): 0)
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- Current
- Review
- Answered
- Correct
- Incorrect
-
Question 1 of 102
1. Question
What is a characteristic of spine-and-leaf architecture?
CorrectIncorrect -
Question 2 of 102
2. Question
Which of the following relate to the Distribution Layer? (Choose two).
CorrectIncorrect -
Question 3 of 102
3. Question
Which protocol is the Cisco proprietary implementation of FHRP?
CorrectIncorrect -
Question 4 of 102
4. Question
Which of the following descriptions are related to Ansible technology? (Choose two).
CorrectIncorrect -
Question 5 of 102
5. Question
What are the two advantages of deploying cloud-based Cisco SD-WAN controllers? (Choose two).
CorrectIncorrect -
Question 6 of 102
6. Question
CorrectIncorrect -
Question 7 of 102
7. Question
A network engineer is configuring an OSPFv2 neighbor adjacency. Which of the following parameters must match regarding OSPF routers? (Choose three).
CorrectIncorrect -
Question 8 of 102
8. Question
From the following descriptions, identify those that pertain to EIGRP. (Choose two)
CorrectIncorrect -
Question 9 of 102
9. Question
Select the correct order of path selection criteria considered by BGP.
CorrectIncorrect -
Question 10 of 102
10. Question
In a typical SD-Access implementation, which type of device would act as a Location ID Separation Protocol (LISP) server for mapping node locations within the network?
CorrectIncorrect -
Question 11 of 102
11. Question
Which plane of operation within the Cisco SD-Access fabric leverages Virtual Extensible LAN (VXLAN) tunneling?
CorrectIncorrect -
Question 12 of 102
12. Question
What component can you design in the SD-Access Overlay solution in order to perform micro-segmentation?
CorrectIncorrect -
Question 13 of 102
13. Question
What 8-bit field exists in IP packet for QoS?
CorrectIncorrect -
Question 14 of 102
14. Question
What Cisco WLAN QoS class is designed for normal traffic?
CorrectIncorrect -
Question 15 of 102
15. Question
Which switch structure stores IP routing-related information, and is also referred to as the Cisco Express Forwarding (CEF) table?
CorrectIncorrect -
Question 16 of 102
16. Question
What is the term used to refer to a broadcast domain within a VXLAN network?
CorrectIncorrect -
Question 17 of 102
17. Question
What component of a LISP architecture identifies the IP address of a router responsible for forwarding traffic to devices within a LISP location?
CorrectIncorrect -
Question 18 of 102
18. Question
In a VRF configuration, you wish view the IP routing table of a virtual router with a VRF instance name of “TENANT-A”. What command would you use?
CorrectIncorrect -
Question 19 of 102
19. Question
What is the output of the following command:
show ip vrf
CorrectIncorrect -
Question 20 of 102
20. Question
What parameter can be different on ports within an EtherChannel?
CorrectIncorrect -
Question 21 of 102
21. Question
Which mode must be used to configure EtherChannel between two switches without using a negotiation protocol?
CorrectIncorrect -
Question 22 of 102
22. Question
Which two statements about EtherChannel technology are true? (Choose two).
CorrectIncorrect -
Question 23 of 102
23. Question
Which two of these statements regarding RSTP are correct? (Choose two).
CorrectIncorrect -
Question 24 of 102
24. Question
Which two states are the port states when RSTP has converged? (Choose two).
CorrectIncorrect -
Question 25 of 102
25. Question
A network engineer needs to verify IP SLA operations on an interface that shows on indication of excessive traffic. Which command should the engineer use to complete this action?
CorrectIncorrect -
Question 26 of 102
26. Question
What command will clear your NAT entries from the translation table?
CorrectIncorrect -
Question 27 of 102
27. Question
Which Cisco IOS command would be used to send NetFlow data to a collection server with the IP address 10.1.1.5 over port 9995?
CorrectIncorrect -
Question 28 of 102
28. Question
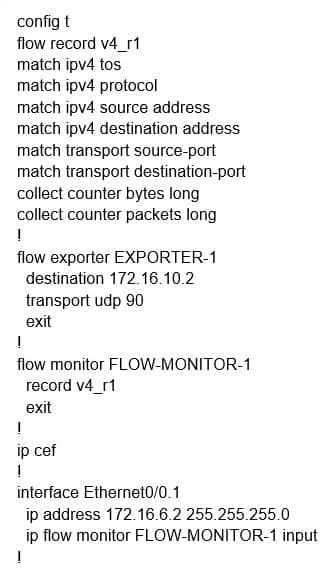
Refer to the exhibit. Why is the remote NetFlow server failing to receive the NetFlow data?
CorrectIncorrect -
Question 29 of 102
29. Question
Which entity within the Control Plane Policing (CoPP) solution allows for traffic filtering and rate limiting?
CorrectIncorrect -
Question 30 of 102
30. Question
Which structure within a Control Plane Policing (CoPP) configuration is used to define the action which should be taken against policed traffic?
CorrectIncorrect -
Question 31 of 102
31. Question
You’re writing a Python script and wish to ask the user the name of the SSID in a wireless network, and you want to assign their response to a variable of ssid. Which command can you use?
CorrectIncorrect -
Question 32 of 102
32. Question
Examine the JSON shown – { “employee”:{ “name”:”John”; “age”:30; “city”:”New York” } } – what is the issue with this syntax?
CorrectIncorrect -
Question 33 of 102
33. Question
Which option about JSON is true?
CorrectIncorrect -
Question 34 of 102
34. Question
Identify the YANG Data Modeling element that represents an attribute of something being modeled.
CorrectIncorrect -
Question 35 of 102
35. Question
When configuring Cisco Embedded Event Manager (EEM) using applets within the CLI, which command keyword defines a condition that we want to take action against?
CorrectIncorrect -
Question 36 of 102
36. Question
With Cisco Embedded Event Manager (EEM), what is used to create policies by using the command line interface (CLI)?
CorrectIncorrect -
Question 37 of 102
37. Question
In a switched environment, what does the IEEE 802.1Q standard describe?
CorrectIncorrect -
Question 38 of 102
38. Question
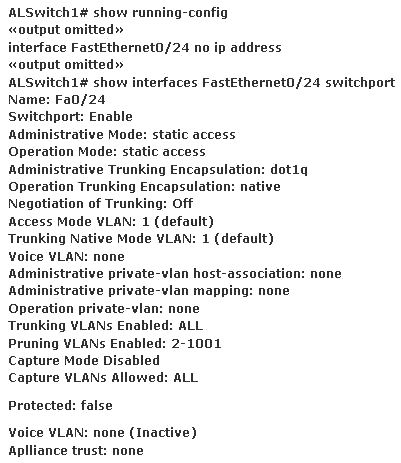
Refer to the exhibit. Switch port FastEthernet 0/24 on ALSwitch1 will be used to create an IEEE 802.1Q-compliant trunk to another switch. Based on the output shown, what is the reason the trunk does not form, even though the proper cabling has been attached?
CorrectIncorrect -
Question 39 of 102
39. Question
How can you fix a recursive routing issue with a GRE tunnel?
CorrectIncorrect -
Question 40 of 102
40. Question
What protocol number is used when you encapsulate a packet with GRE?
CorrectIncorrect -
Question 41 of 102
41. Question
An administrator intends to configure an IPSec solution that provides ESP with integrity protection, but not confidentiality protection. Which of the following AES modes of operation would meet this integrity-only requirement?
CorrectIncorrect -
Question 42 of 102
42. Question
What IPsec technology allows the exchange of a shared secret key over an unsecured medium using a symmetric key exchange?
CorrectIncorrect -
Question 43 of 102
43. Question
What port number is used by Network Time Protocol (NTP)?
CorrectIncorrect -
Question 44 of 102
44. Question
Which command must be entered when a device is configured as an NTP server?
CorrectIncorrect -
Question 45 of 102
45. Question
After configuring ERSPAN in Cisco IOS, what command is necessary in order to enable the ERSPAN configuration on a selected interface?
CorrectIncorrect -
Question 46 of 102
46. Question
By default, which type of traffic does SPAN monitor in Cisco IOS?
CorrectIncorrect -
Question 47 of 102
47. Question
An engineer configured the wrong default gateway for the Cisco DNA center enterprise interface during the install. Which command must the engineer run to correct the configuration?
CorrectIncorrect -
Question 48 of 102
48. Question
How does Cisco DNA Center gather data from the network?
CorrectIncorrect -
Question 49 of 102
49. Question
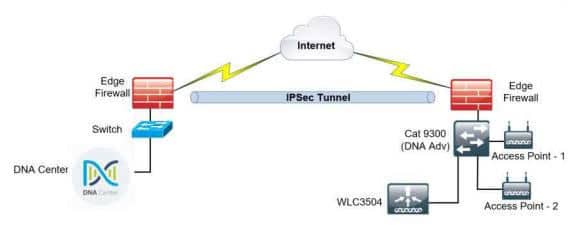
Refer to the exhibit. A network administrator is discovering a Cisco Catalyst 9300 and a Cisco WLC 3504 in Cisco DNA Center. The Catalyst 9300 is added successfully However the WLC is showing [ error “uncontactable” when the administrator tries to add it in Cisco DNA Center. Which action discovers WLC in Cisco DNA Center successfully?
CorrectIncorrect -
Question 50 of 102
50. Question
NETCONF supports what type of data formatting?
CorrectIncorrect -
Question 51 of 102
51. Question
If a notice-level message is sent to a syslog server, which event has occurred?
CorrectIncorrect -
Question 52 of 102
52. Question
What command instructs the device to timestamp Syslog debug messages in milliseconds?
CorrectIncorrect -
Question 53 of 102
53. Question
Which Cisco IOS command allows us to specifically turn off conditional debugging that has been put in place for the GigabitEthernet 0/1 interface of a router?
CorrectIncorrect -
Question 54 of 102
54. Question
Which command is used to turn off all possible debugging in Cisco IOS?
CorrectIncorrect -
Question 55 of 102
55. Question
What are two requirements for an HSRP group? (Choose two).
CorrectIncorrect -
Question 56 of 102
56. Question
Which of the following is true of VRRP but not true of HSRP?
CorrectIncorrect -
Question 57 of 102
57. Question
Which MAC address is recognized as a VRRP virtual address?
CorrectIncorrect -
Question 58 of 102
58. Question
During an inter-controller Layer 3 roam, how does Cisco refer to the target WLC?
CorrectIncorrect -
Question 59 of 102
59. Question
What multicast routing protocol must use an RP in its operation?
CorrectIncorrect -
Question 60 of 102
60. Question
What is a difference between local AP mode and FlexConnect AP mode?
CorrectIncorrect -
Question 61 of 102
61. Question
Which of the following are valid options for AP WLC discovery? (Choose three)
CorrectIncorrect -
Question 62 of 102
62. Question
The SNR in wireless networking is calculated using the transmit power and what other value?
CorrectIncorrect -
Question 63 of 102
63. Question
Which native extensible authentication protocol (EAP) type uses certificates for mutual authentication?
CorrectIncorrect -
Question 64 of 102
64. Question
Which piece of the Network Access Control (NAC) architecture receives extensible authentication protocol (EAP) packets and translates those into RADIUS packets?
CorrectIncorrect -
Question 65 of 102
65. Question
What Cisco command shows you the status of an 802.1x connection on interface gi0/1?
CorrectIncorrect -
Question 66 of 102
66. Question
Which type of web-based authentication (WebAuth) leverages an external AAA server that works as a centralized RADIUS database, such as Cisco Identity Services Engine (ISE)?
CorrectIncorrect -
Question 67 of 102
67. Question
An engineer must configure a WLAN using the strongest encryption type for WPA-2 PSK. Which cipher fulfills the requirement?
CorrectIncorrect -
Question 68 of 102
68. Question
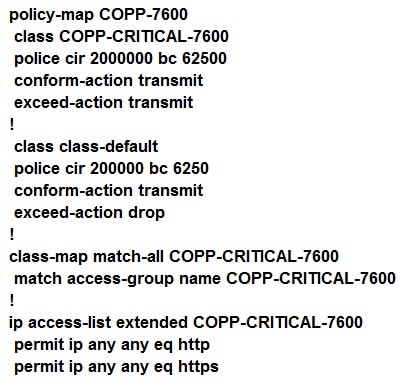
Refer the exhibit. BGP is flapping after the CoPP policy is applied. What are the two solutions to fix the issue? (Choose two).
CorrectIncorrect -
Question 69 of 102
69. Question
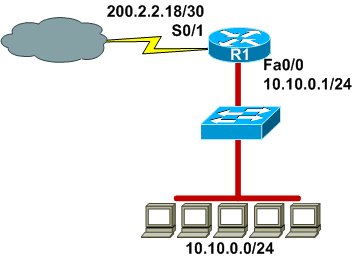
Refer to the exhibit. A company wants to use NAT in the network shown. Which commands will apply the NAT configuration to the proper interfaces? (Choose two).
CorrectIncorrect -
Question 70 of 102
70. Question
A user configured OSPF in a single area between two routers. A serial interface is connecting the two routers. If a user types the command “show ip ospf interface” on either router, which OSPF network type will be assigned to the serial interface connecting to the other OSPF router?
CorrectIncorrect -
Question 71 of 102
71. Question
OSPF can perform route summarization on an ASBR or on an ABR. What command is used to summarize routes on an ASBR?
CorrectIncorrect -
Question 72 of 102
72. Question
OSPF routing uses the concept of areas. What are the characteristics of OSPF areas? (Choose three).
CorrectIncorrect -
Question 73 of 102
73. Question
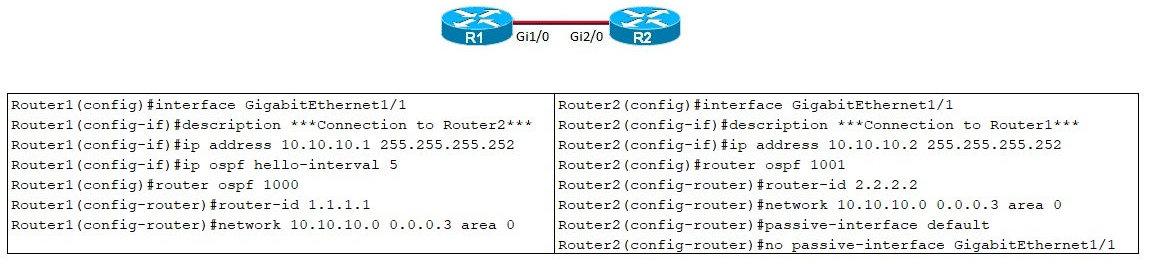
Refer to the exhibit. After the configuration is applied, the two routers fail to establish an OSPF neighbor relationship. what is the reason for the problem?
CorrectIncorrect -
Question 74 of 102
74. Question
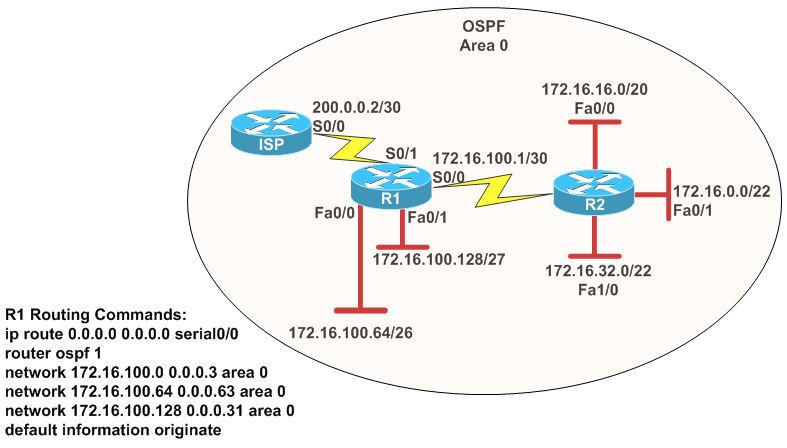
Refer to the exhibit. Assume that all router interfaces are operational and correctly configured. In addition, assume that OSPF has been correctly configured on router R2. How will the default route configured on R1 affect the operation of R2?
CorrectIncorrect -
Question 75 of 102
75. Question
An inbound access list has been configured on a serial interface to deny packet entry for TCP and UDP ports 21, 23, and 25. What types of packets will be permitted by this ACL? (Choose three).
CorrectIncorrect -
Question 76 of 102
76. Question
A company is practicing server virtualization by running the hypervisor software directly on top of the hardware platform. What type of hypervisor is this?
CorrectIncorrect -
Question 77 of 102
77. Question
What asset tag technology can function with the location services of Cisco WLAN technologies?
CorrectIncorrect -
Question 78 of 102
78. Question
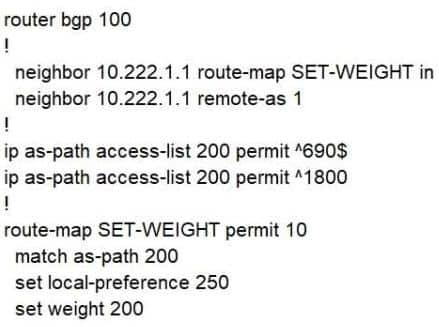
Refer to the exhibit. A router receives BGP routing updates from multiple neighbors to routers in AS690. Why does the router send traffic that is destined to AS690 to a neighbor other than 10.222.1.1?CorrectIncorrect -
Question 79 of 102
79. Question
Which effect does the aaa new-model configuration command have?
CorrectIncorrect -
Question 80 of 102
80. Question
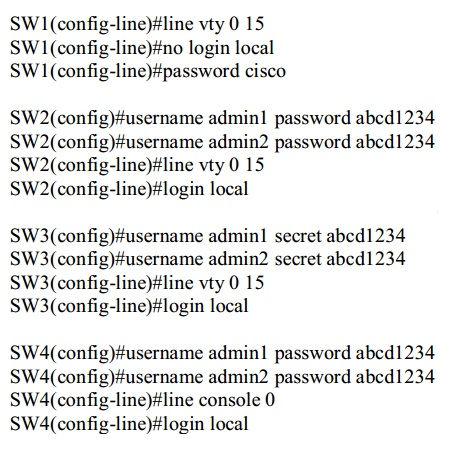
Refer to the exhibit. An administrator configures four switches for local authentication using passwords that are stored in a cryptographic hash. The four switches must also support SSH access for administrators to manage the network infrastructure. Which switch is configured correctly to meet these requirements?
CorrectIncorrect -
Question 81 of 102
81. Question
Which two keying mechanisms are available within MACsec? (Choose two).
CorrectIncorrect -
Question 82 of 102
82. Question
What technology available for the LAN today is similar to IPsec but operates at Layer 2?
CorrectIncorrect -
Question 83 of 102
83. Question
Northbound Interfaces (NBIs) are what type of Application Programing Interfaces (APIs)?
CorrectIncorrect -
Question 84 of 102
84. Question
What does traffic shaping do to reduce congestion in a network?
CorrectIncorrect -
Question 85 of 102
85. Question
Which API is used in controller based architecture to interact with edge devices?
CorrectIncorrect -
Question 86 of 102
86. Question
Which if the following is NOT a Rapid PVST+ port state?
CorrectIncorrect -
Question 87 of 102
87. Question
Which element of the SD-WAN solution from Cisco Systems represents the controller responsible for the management of the solution?
CorrectIncorrect -
Question 88 of 102
88. Question
You are interested in using a new security model in your Enterprise network; one that is not based strictly on Layer 2 or Layer 3 addressing. What component of the SD-Access solution accommodates this?
CorrectIncorrect -
Question 89 of 102
89. Question
What SD-Access device is responsible for de-encapsulating LISP traffic for transport to non-LISP sites?
CorrectIncorrect -
Question 90 of 102
90. Question
What technology uses HTTP methods to provide CRUD operations on a conceptual datastore containing YANG-defined data?
CorrectIncorrect -
Question 91 of 102
91. Question
What REST API response code would you expect to see if there was a problem with authorization during the REST API usage?
CorrectIncorrect -
Question 92 of 102
92. Question
You want to improve the performance of roaming in your FlexConnect infrastructure. Specifically, you want to employ the Fast Transition feature. What technology permits this?
CorrectIncorrect -
Question 93 of 102
93. Question
You are preparing to add a new node to your Cisco DNA Center cluster. What command should you run to verify your configuration before adding the new node?
CorrectIncorrect -
Question 94 of 102
94. Question
What SD-WAN component performs the initial authentication of WAN edge devices?
CorrectIncorrect -
Question 95 of 102
95. Question
What is the multicast address used by HSRPv2?
CorrectIncorrect -
Question 96 of 102
96. Question
Which of the following is not an Authentication Key Management option for WLAN security?
CorrectIncorrect -
Question 97 of 102
97. Question
Which of the following statements regarding Access Control Lists in Cisco networking are true? (Choose 3)
CorrectIncorrect -
Question 98 of 102
98. Question
You are interested in providing your WLC address to your Lightweight Access Point using DHCP. What option is used for this?
CorrectIncorrect -
Question 99 of 102
99. Question
Which of the following statements are valid considering fabric-mode access points in the SD-Access solution? (Choose 2)
CorrectIncorrect -
Question 100 of 102
100. Question
Which type of WiFi antenna is not directional?
CorrectIncorrect -
Question 101 of 102
101. Question
What form of QoS is most likely to cause TCP retransmissions?
CorrectIncorrect -
Question 102 of 102
102. Question
When using Cisco DNA Center, templates you create with the Template Editor are associated with what DNA Center component?
CorrectIncorrect