ISE Authentication Policies
The ISE is a real workhorse in the network today. Thanks to many different types of policies available on the Cisco ISE, the device can help with mobile devices, guests, high security devices, low security devices, compliance, posture, and more. But at the heart of the ISE is authentication policies.
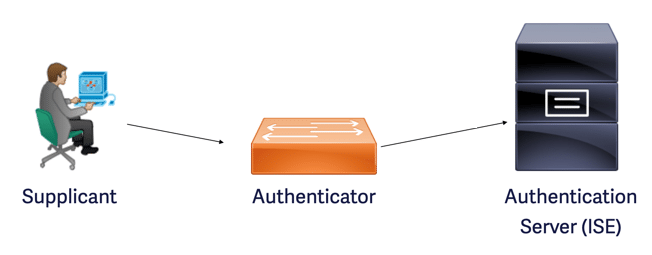
Thanks to the authentication policy, the ISE can quickly drop traffic that is not a supported protocol or that is malformed. Should the traffic be permitted, the ISE can quickly validate the credentials and then either deny the access attempt or pass the information on to the authorization processes of the ISE.
Notice how a carefully crafted authentication policy can enforce many important aspects of security. This policy can ensure the following:
- The authentication policy can ensure that legacy or insecure protocols are not accepted. Notice that this not only improves the security of our network, but it also ensures the resources of the ISE are not bogged down by analyzing packets that are not even supported in our organization. If you have decided on the use of EAP-TLS in your network, you can ensure that only these packets are actually analyzed and processed by the ISE. You might have a group of misconfigured clients that are sending packets to the ISE. These packets can be ignored as they should be!
- The authentication policy permits the USE to select the correct identity store. Remember, we can configure the ISE to use internal identities and many different potential external identity stores. We might have AD, several LDAP stores, and certificate stores. The authentication policy can help ensure the correct identity store is selected for the authentication of the user. It does this by examining key attributes in the information sent from the authenticator about this client.
- The authentication policy also ensures the proper validation of credentials. For example, if a certificate is being used for authentication, we need to ensure that this certificate is correctly formed and that it contains the correct information we need for authentication purposes. We need to ensure that the certificate has not expired or been revoked. The authentication policy can trigger all of these important checks for us.
- Of course, another important job of the authentication policy is to forward the requests to the authorization engine of the ISE.
Policy sets of the ISE allow us to configure authentication policies for the many networks that might exist in our enterprise. For example, you can configure the appropriate authentication policy in a policy set matching a certain SSID in your organization. This targeted approach is a dramatic improvement in the latest ISE designs compared to earlier versions where there was one, single overarching authentication policy that applied to absolutely all traffic forwarded to the ISE.
Interested in learning more about the ISE, be sure to check out the on-demand CCIE Mastering ISE course here at lammle.com. This course is currently under development and will finish around March 15, 2021. Like all new courses in the lammle.com library, this course emphasizes a hands-on training experience with ISE. Students are walked through the building of their own practice lab step by step.