Worst Cyber Attack in History hits U.S.
Microsoft Exchange servers have been exploited by four zero-day flaws.
On March 2, Microsoft warned that the four zero-day listed as CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 — were being exploited, and the vulnerabilities could be used to compromise servers running Exchange Server 2013, 2016, and 2019 software. Probably hundreds of thousands of Exchange servers have been compromised by the time you are reading this.
- CVE-2021-26855 is a server-side request forgery (SSRF) vulnerability in Exchange which allowed the attacker to send arbitrary HTTP requests and authenticate as the Exchange server.
- CVE-2021-26857 is an insecure deserialization vulnerability in the Unified Messaging service. Insecure deserialization is where untrusted user-controllable data is deserialized by a program. Exploiting this vulnerability gave HAFNIUM the ability to run code as SYSTEM on the Exchange server. This requires administrator permission or another vulnerability to exploit.
- CVE-2021-26858 is a post-authentication arbitrary file write vulnerability in Exchange. If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. They could authenticate by exploiting the CVE-2021-26855 SSRF vulnerability or by compromising a legitimate admin’s credentials.
- CVE-2021-27065 is a post-authentication arbitrary file write vulnerability in Exchange. If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. They could authenticate by exploiting the CVE-2021-26855 SSRF vulnerability or by compromising a legitimate admin’s credentials.
When these CVE’s are chained together, these vulnerabilities are known as ‘ProxyLogon’ and allow the threat actors to perform remote code execution on publicly exposed Microsoft Exchange servers utilizing Outlook on the web (OWA).
Completely shocking (yea right) is the fact that Microsoft has attributed the attacks to a Chinese state-sponsored advanced persistent threat (APT) group known as HAFNIUM.
When disclosing these vulnerabilities, Microsoft provided a list of commands that Exchange administrators could use to check if a server was hacked. These commands would need to be executed manually to check for indicators of compromise (IOC) in Exchange HttpProxy logs, Exchange log files, and Windows Application event logs. Yesterday, Microsoft released a PowerShell script on the Microsoft Exchange support engineer’s GitHub repository named Test-ProxyLogon.ps1 to automate these tasks for the administrator.
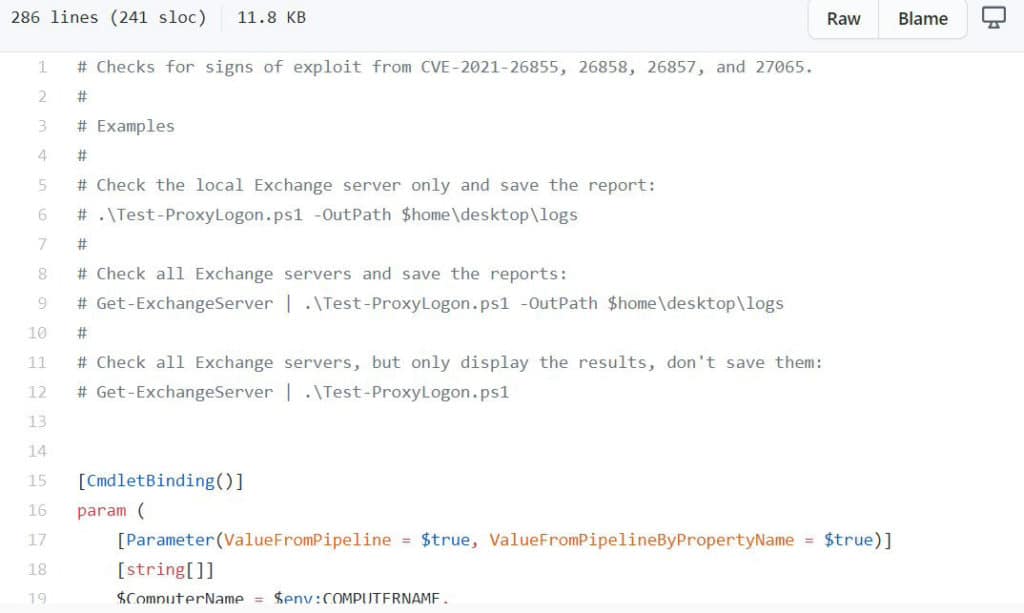
Microsoft provides the following instructions on using the script to check a single Microsoft Exchange server or all servers in your organization.
To check all Exchange servers in your organization and save the logs to the desktop, you would enter the following command from Exchange Management Shell:
Get-ExchangeServer | .\Test-ProxyLogon.ps1 -OutPath $home\desktop\logs
If you only want to check the local server and save logs, you would enter the following command:
.\Test-ProxyLogon.ps1 -OutPath $home\desktop\logs
Finally, to only test the local server and display the results without saving them, you can run the following command:
.\Test-ProxyLogon.ps1
Patch your Exchange: March 2021 Exchange Server Security Updates
Microsoft has released a set of out of band security updates for vulnerabilities for the following versions of Exchange Server:
- Exchange Server 2013
- Exchange Server 2016
- Exchange Server 2019
Security updates are available for the following specific versions of Exchange:
- Exchange Server 2010 (update requires SP 3 or any SP 3 RU – this is a Defense in Depth update)
- Exchange Server 2013 (update requires CU 23)
- Exchange Server 2016 (update requires CU 19 or CU 18)
- Exchange Server 2019 (update requires CU 8 or CU 7)
“Because we are aware of active exploits of related vulnerabilities in the wild (limited targeted attacks), our recommendation is to install these updates immediately to protect against these attacks.”